As nearly every business industry transitioned to digitally-powered operations, the demand for cybersecurity specialists skyrocketed. To the point that it overweights the supply.
For the past five years, organizations have been struggling to fill in all the open security roles. According to an annual (ISC)² Cyber Workforce Study, over 2.7 million security positions remain unfilled globally. As TechRepublic further reports because of that gap 62% of employers report heavier workload for staff and 38% name higher worker burnout rates.
What does all of the above mean for you? If you are just entering the workforce or already worked in cybersecurity for several years, there will be no shortage of jobs. Yet, the working environments can differ a lot. Clearly, understaffed companies will expect the new hires to put in more hours to contain all the fires.
So how do you ensure that you land a job with an employer offering not just stellar compensation, but also a proper work-life balance? First of all, by doing company research. Secondly, by writing an attractive cybersecurity resume that lands you multiple offers to cherry-pick.
This post provides several actionable tips, followed by a cybersecurity resume sample.
Get the Basics Covered First
What sets a good resume from a mediocre one? Three things:
- Proper structure
- Optimal formatting
- Customization
All resumes need to have three well-formatted, skimmable sections. A resume header that includes your personal information, contact details, website, and perhaps a quick professional tagline.
Then a work experience section. Include your most recent (and relevant) work entries. For each, write a quick summary, followed by a bullet point list of main duties and accomplishments.
Finally, round it up with a short education experience section, where you list your degree and other industry certifications.
Once you are done, go to a job ad you are eying and check the “candidate’s requirements” section. Verify if you are using the same terms and phrases in your resume. If not, add the missing ones.
Highlight Your Soft Skills
As an experienced cybersecurity candidate, it can be tempting to highlight your profound technical skills. Sure, most employers want to know whether you are experienced in conducting forensic investigations or using the latest SIEM/SOAR tools.
But many also want to ensure that you are a good team player. After all, most cybersecurity people are hired as a part of a SOC unit, where collaboration and strong team alignment are essential. Also, cybersecurity people often need to report to non-technical c-suite on the state of security, plus educate other employees on the latest best practices.
So do bring up some of your soft skills too. Show that you are not only proficient when it comes to tech, but also efficient in communication with others.
Showcase Your Conceptual Skills
To stay one step ahead of attackers, cybersecurity professionals need to think creatively. If you are after a senior-level position of a Threat Investigator or SOC manager, show that you have strong problem-solving and analytical skills. Similarly, it’s always worth mentioning your ability to independently analyze data and develop hypotheses based on it.
To contextualize these skills on your resume, try adding a quick example such as this one:
“Proposed and implemented a new identity management policy after conducting an in-depth audit of user behaviors. It reduced false positive alerts by 25%”.
Resume Sample for Cyber Security (Word version)
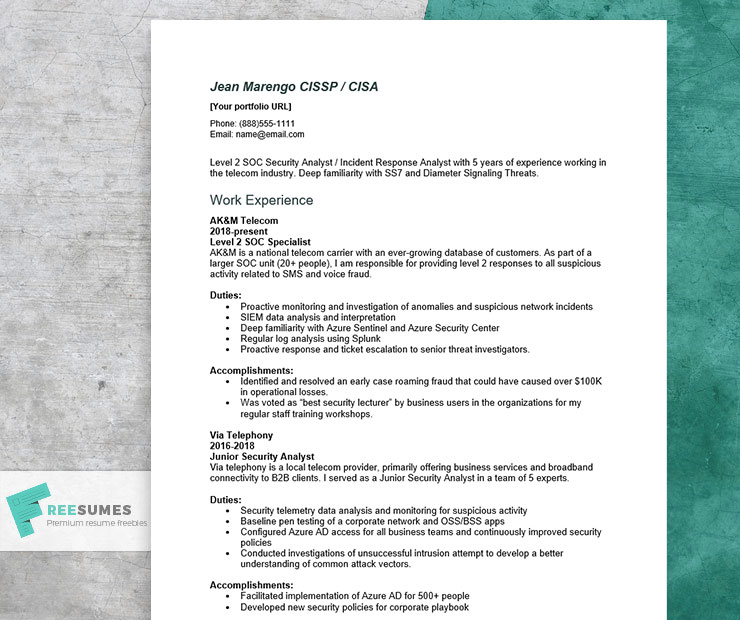
Below is a sample resume for a mid-career SOC analyst, seeking a position in the telecom industry.
Download resume example (.docx)
Cyber Security Resume Example (text version)
Jean Marengo CISSP / CISA
[your portfolio website URL]
Level 2 SOC Security Analyst / Incident Response Analyst with 5 years of experience working in the telecom industry. Deep familiarity with SS7 and Diameter Signaling Threats.
Work Experience
AK&M Telecom
2018-present
Level 2 SOC Specialist
AK&M is a national telecom carrier with an ever-growing database of customers. As part of a larger SOC unit (20+ people), I am responsible for providing level 2 responses to all suspicious activity related to SMS and voice fraud.
Duties:
- Proactive monitoring and investigation of anomalies and suspicious network incidents
- SIEM data analysis and interpretation
- Deep familiarity with Azure Sentinel and Azure Security Center
- Regular log analysis using Splunk
- Proactive response and ticket escalation to senior threat investigators.
Accomplishments:
- Identified and resolved an early case roaming fraud that could have caused over $100K in operational losses.
- Was voted as “best security lecturer” by business users in the organizations for my regular staff training workshops.
Via Telephony
2016-2018
Junior Security Analyst
Via telephony is a local telecom provider, primarily offering business services and broadband connectivity to B2B clients. I served as a Junior Security Analyst in a team of 5 experts.
Duties:
- Security telemetry data analysis and monitoring for suspicious activity
- Baseline pen testing of a corporate network and OSS/BSS apps
- Configured Azure AD access for all business teams and continuously improved security policies
- Conducted investigations of unsuccessful intrusion attempt to develop a better understanding of common attack vectors.
Accomplishments:
- Facilitated implementation of Azure AD for 500+ people
- Developed new security policies for corporate playbook
Education
University of Florida
BS – Computer Science
June 2016
Dean’s List
Professional certifications
- Certified Information Systems Auditor (CISA) credential issued by ISACA in November 2021.
- Certified Information Systems Security Professional (CISA) credential issued by (ISC)² in April 2020.
- Microsoft Azure Security Engineer Associate credential issued by Microsoft in July 2017.
Final Tip: Provide Background Into Your Experience
Every industry faces somewhat different security threats and varying degrees of regulatory requirements. So it follows that employers are leaning more towards security “specialists” with relevant industry knowledge over “generalists”. You should always mention if you are familiar with some of the unique challenges the employer’s industry faces. Plus provide some background into how you’ve previously tackled these hurdles.






